National Interdisciplinary Center for Cyber Security and Cyber Defence of Critical Infrastructures(C3i)
Since SEBI funded the C3i Center at IIT Kanpur in March 2017, C3i center1 has developed into a leading research, education, and technology innovation center in the space of cyber security and cyber defense of critical infrastructure and has installed industry-scale testbeds for vulnerability assessment and penetration testing, developing cyber security mitigation techniques and tools, and testing their efficacy. Currently the C3i Center has the test-beds for
- SCADA/PLC based Power distribution Automation
- Solar and diesel generation and synchronization test bed to the institute grid
- SCADA/PLC based Power Transmission Testbed
- DCS Testbed
- 4 stage SCADA monitored PLC controlled Water treatment plant testbed
- Multi-stage PLC controlled Industrial manufacturing testbeds, and
A few other infrastructures equipment at C3i – a. Control system for power testbed, b. Smart load bank for power testbed, and c. Portable Educational Kits for SCADA/PLC Security Education. C3i center has designed and developed these “Portable kits” to fulfil an immediate need of “Patch testing” and hands on “OT security training.” These kits give exposure to various industrial protocols.
Along with the full scaled industrial testbeds, C3i center has a strong and dedicated team of researchers working for deployment of honeypots for deceiving attackers, building malware analysis framework for file analysis, VAPT of IT and OT components in and outside the center, and designing secure UI/UX components for our customers and industrial partners.
A few Major Achievements :
- Vulnerability Assessment
Team C3i has successfully identified many vulnerabilities in the products and the systems to assess the hardware and software pertaining to OT in ICS system. A few of them already received international recognition. The latest of them is – CVE ID: CVE-2020-7536 (https://nvd.nist.gov/vuln/detail/CVE-2020-7536)15+ responsible
disclosures
8 CVEs - Publications
A few Major Achievements :Papers:70+ International Conference,
Journal Papers, Book Chapters, Book40+ Master Thesis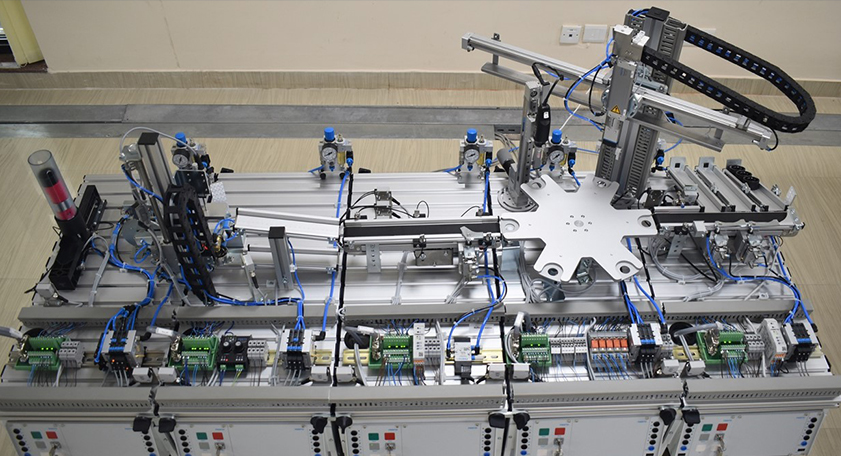 Industrial control testbed c3i
Industrial control testbed c3i Power transmission testbed c3i
Power transmission testbed c3i - Solutions (C3i Center Developed Various Technology Solutions which can be further developed into Products)
- Malware Analysis: C3i center offers an indigenous web-based malware analysis tool. This tool can detect and classify malware in near real-time. The tool contains various types of analysis for various filetypes but not limited to PE, ELF, APK, doc/docx, PDF, XLS, PNG, HTML, JPEG, etc. It uses an ensemble of machine learning models. C3i center analyzed 2,423,124 Malware samples using various methodologies – static, dynamic, hybrid, and memory analysis. The tool gives a promising accuracy for the file types mentioned.
Total malware files analyzed - 2423124 - Honeypot:C3i center has deployed honey network composed of several honeypots for both IT and OT environment to deceive the attackers. Types of honeypots deployed at various locations using cloud environment – HTTP, Modbus, Telnet, SNMP, FTP, BACnet, S7Comm, TFTP, and IPMI. C3i center also progressed in developing a Security Orchestration and Automated Response (SOAR) for deploying honeypots based on attacker behavior. The engine can dynamically deploy desired honeypots.
- ReconAID: It is a reconnaissance automation tool developed at C3i center which can collect information such as technology stack, visual recon, network map, open port, running services, and versions, etc. It can collect hidden endpoints and directories. It can also scan and search Hidden endpoints and tokens in JS files and Github. It has used publicly available exploit engines to gather critical information from Shodan, Censys, Securitytrail, Binaryedge, crt.sh, etc. It has the functionality to search any vulnerable service in the CVE engine and has a reporting and notification feature. It gives a statistic related to total scanned domains, endpoints discovered, ports found, subdomains found, etc.
- Network Intrusion Detection System (NIDS): C3i center’s NIDS has two components – Infrastructure Mapper & Processor (IMP) and Data Acquisition, Analysis & Monitoring Server (DAAMS). IMP and DAAMS is a customized solution to enhance the cybersecurity of operational technologies (OT) networks. The solution auto-discover of all IoT and ICS assets and maintains a constantly up-to-date inventory of them along with associated vulnerabilities, a detailed dynamic network topology, classification of logs via machine learning, network intrusion results, etc. This application can read packets (passive monitoring) from the network and extract useful information based on assets’ information. This solution is still under improvisation.
- Intrusion Detection System (IDS): C3i center has developed a web - IDS to monitor all cyber events on C3i’s web servers. It’s an AI-ML empowered solution which may help any SOC (Security Operation Center) to obtain full visibility, situational awareness, and actionable threat intelligence. This system can be customized for other facilities outside the center as well. The dashboard gives statistics about the types of attacks – SQLi, XSS, CSRF, etc. An IDS for ICS systems are also developed which is a light-weight program that runs on the PLC and detects any data tampering including false data injection attacks.
- Formal Verification: To compute the risk posed to individual nodes due to existing vulnerabilities, C3i used a model checker to compute the probability scores for all nodes in any network on which vulnerability scanning tools found known vulnerabilities. C3i used the probabilistic model checking tool PRISM to compute threat scores. It was a collaborative project with Hitachi India R&D.
- Cryptographic Hardware (Kryptoceler): An FPGA based hardware accelerator for packet level encryption reduces the workload and speed up the throughput of network applications. Stronger security assurance is grounded in the root-of-trust for software, firmware and hardware that performs reliable security operations. The hardware of “Kryptoceler” is tested for a back-door or a Trojan to ensure that there is no point of vulnerability on the board. With this foundation of trust, software and firmware solutions for cryptographic cores are implemented on the hardware
- Malware Analysis: C3i center offers an indigenous web-based malware analysis tool. This tool can detect and classify malware in near real-time. The tool contains various types of analysis for various filetypes but not limited to PE, ELF, APK, doc/docx, PDF, XLS, PNG, HTML, JPEG, etc. It uses an ensemble of machine learning models. C3i center analyzed 2,423,124 Malware samples using various methodologies – static, dynamic, hybrid, and memory analysis. The tool gives a promising accuracy for the file types mentioned.


Collaborations:
Since SEBI funded the C3i Center at IIT Kanpur in March 2017, C3i center1 has developed into a leading research, education, and technology innovation center in the space of cyber security and cyber defense of critical infrastructure and has installed industry-scale testbeds for vulnerability assessment and penetration testing, developing cyber security mitigation techniques and tools, and testing their efficacy. Currently the C3i Center has the test-beds for
C3i center has partnered with various private and public sector agencies and bodies to strengthen the cyber security posture in India. A lot of interaction with government agencies such as the National Cyber Security Coordinator, Central Electric Authority, National Thermal Power Corporation, National Highways Authority of India, Tehri Hydro Development Corporation India Limited (Tehri, Uttarakhand), Indian Ports Association, CySeck, BEL Ghaziabad, are on-going. Several industries, such as HCL, Schneider Electric, Tech-Mahindra, LTTS, SMC have been interacting quite often.
Education, Awareness & Events:
C3i center also promotes awareness and education in cybersecurity. A few training sessions have been organized for NPTI (National Power Training Institute) and NHAI. C3i, IIT Kanpur, in association with TalentSprint, has designed a six-month Advanced Certification Program in Cyber Security and Cyber Defense for current and aspiring professionals from various organizations who are keen to explore and learn the latest trends in Cyber Security Technologies. Three cohorts have been completed and the fourth cohort is ongoing and approximately 125 professionals were certified. TalentSprint launched a fresh graduate cyber security education program online with C3i Center which will be opened to participants who are within 2 years of their graduation – and want to enter in the cyber security field. C3i center also started a Blockchain Technology Certification program with Simplilearn – another online educational technology platform. The IITK Senate also approved M.Tech. and M.S. in cyber security program, and e-Masters (fully online) in Cyber Security. C3i center has offered internships to more than 50 students across India.
A yearly cyber-security competition event CSAW, in cooperation with New York University, has been an on-going activity. C3i center has exhibited it’s research at various platforms like NULLCON conference, DSCI summit, INDISEC summit, etc.
Startups:
Along with 12 other startups in various domains of cyber security which were incubated at IIT Kanpur, a start-up in deception technology, which is a part of C3i center has been incubated under the C3iHub Prayas and Nidhi Prayas program.